The vast majority of cyber security attacks happen through email. We’ve compiled a list of email security tips to protect your organisation’s email accounts from hackers.
Did you know that 92% of all cyber security attacks on enterprises start with an email?
According to a 2018 report by Cofense, email delivers 92% of all cyber attacks to organisations, with over 50% of malicious emails being a “phishing” attack. These figures are consistent with a Deloitte report’s findings, which show that 91% of all attacks begin with a phishing email to an unsuspecting email user.
What Is a Phishing Email?
Phishing is a commonly used method of cyber attack where disguised email carries viruses, malicious software and links to fraudulent sites.
In recent years, phishing emails have become more convincing than ever, addressing recipients by name and using the credentials of an organisation they interact with, such as a bank, healthcare provider and even HMRC. Here’s an example of a very convincing phishing email from “Microsoft” claiming “Unusual sign-in activity”.
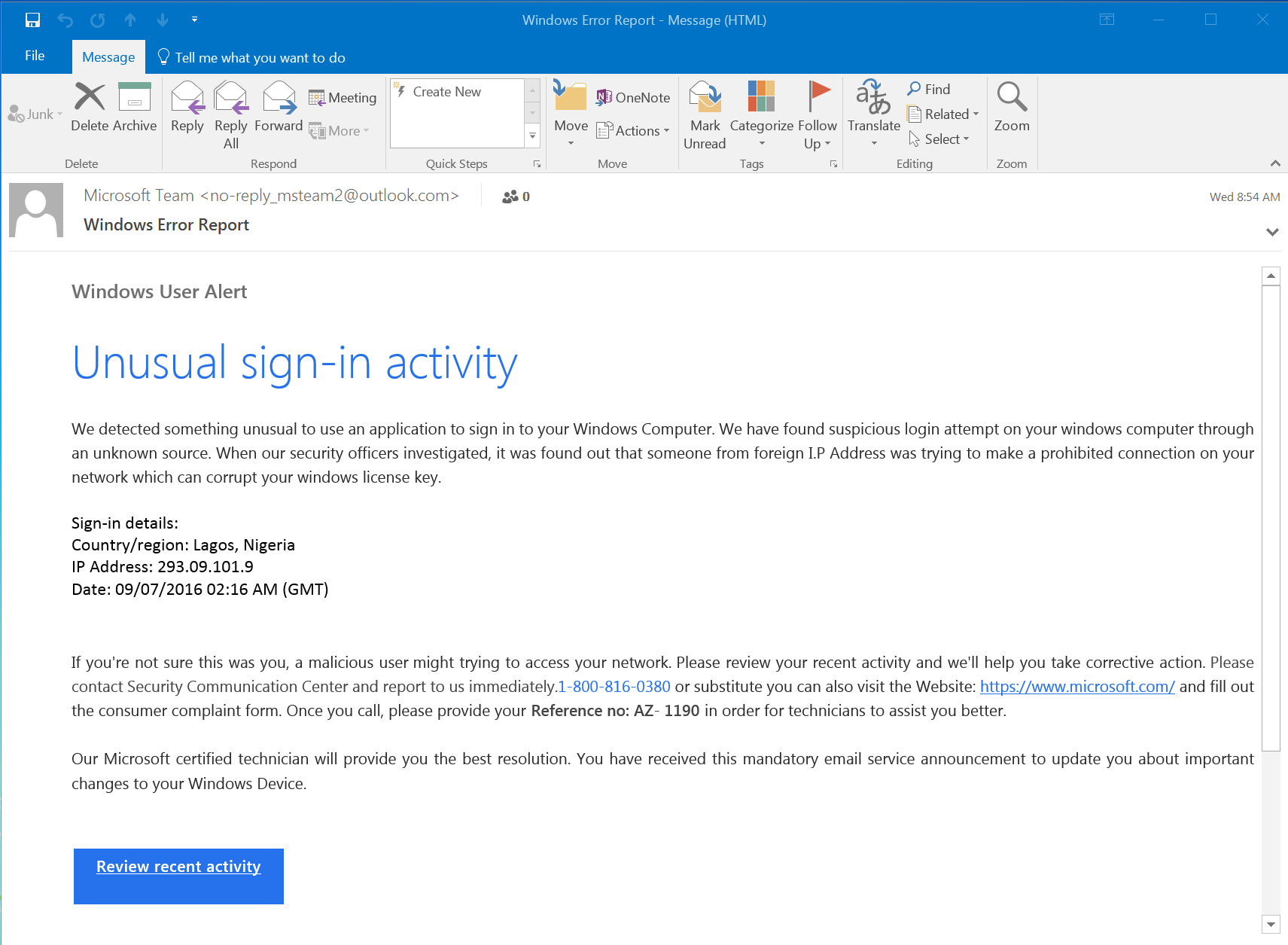
Image Source: Phishing.org
A phishing email often asks the recipient to resolve a problem, such as alleged credit card fraud, or claim a prize (such as a voucher) from a store they frequent. The email can have a dummy phone number that connects the recipient to a scam call centre or carry a link that directs the user to a spoof website — a complete clone of a legitimate website, complete with images and a log-in window.
Once a user provides their username and password to the fraudulent site, an attacker will use those stolen credentials to remotely log-in to that user’s email. Then it’s open season; the attacker can download personal financial information, social media logins and personal messages.
This is bad enough for regular consumers, but the effects can be more devastating if the phishing email compromises a business email account carrying sensitive corporate information.
Enter the world of business email compromise, where fraudsters use phishing emails to ask suppliers to send money to their account or pose as the company’s CEO to get their accounting departments to disburse money.
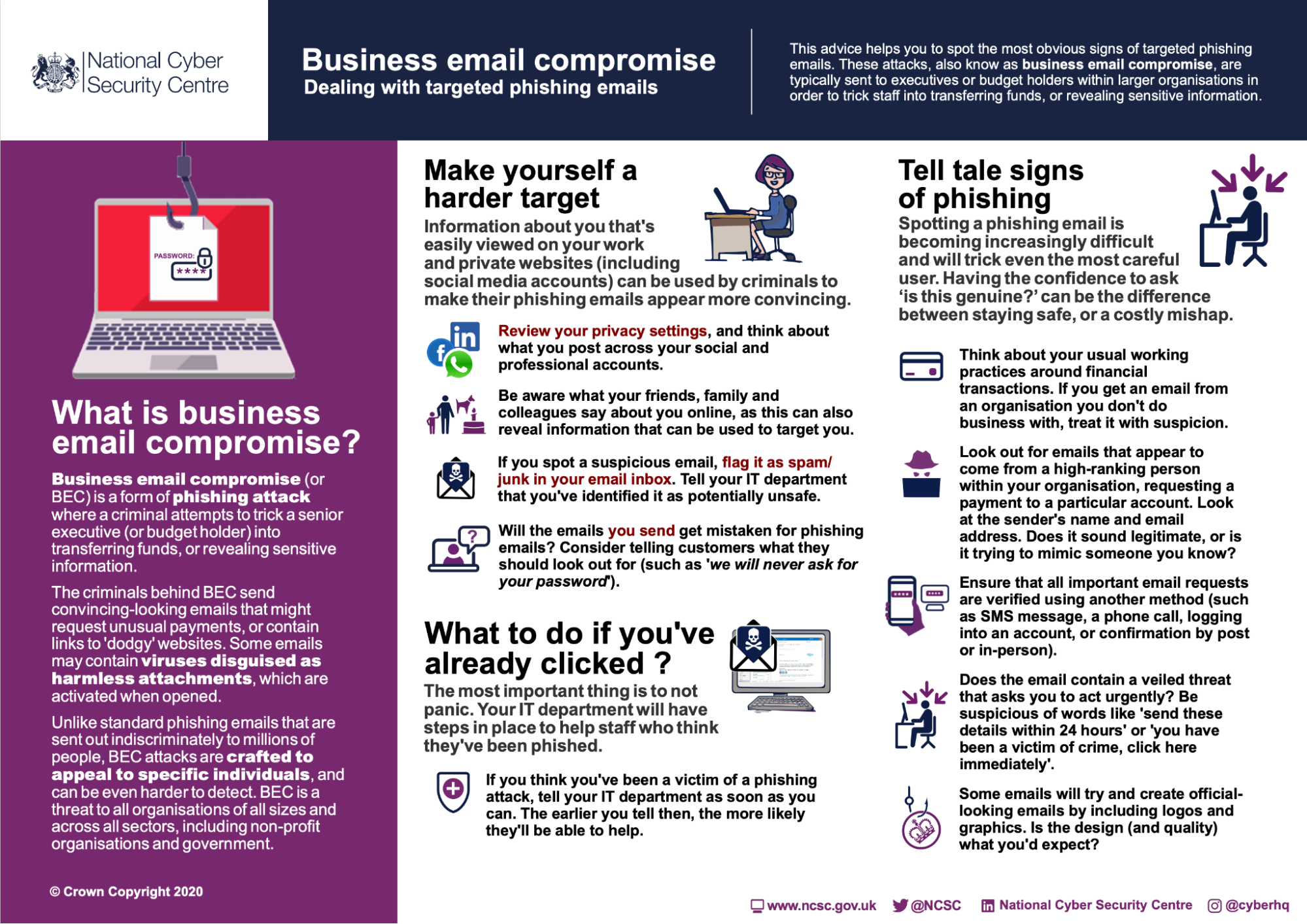
Image Source: National Cyber Security Centre
6 Common Scenarios of Email Attacks Aimed at Businesses
Over the last few years, the team at Optimising IT has been called in to help organisations of all sizes and industries with their cyber security following a breach.
It’s unfortunate, not only that the breach occurred but that you could have greatly reduced the risk of it happening in the first place with simple steps — often using existing, properly configured solutions.
Compromised email accounts are perhaps the most common IT issue we see. While adopting cloud-based solutions and remote access to on-premise email platforms is great for productivity and resilience, it exposes your business to cyber attacks if your cloud systems are not appropriately secured.
Once an attacker has gained access to a victim’s email, we have commonly found the following scenarios:
- Forwarding rules are set up to capture specific types of emails, such as invoices or requests for payment.
- The attackers set up rules to prevent either outgoing or incoming payments from reaching the compromised user’s email account.
- Once a payment request has been captured, the attackers either send out or release to the compromised user a modified payment request with new bank account details.
- Attackers direct emails to the compromised employee, requesting a transfer of funds to a new account.
- Attackers use the compromised email account to send phishing emails to other people in the organisation or different organisations from a legitimate email source.
- Attackers use a compromised email account to get other individuals inside or outside the organisation to download a malicious file. This file has often contained a banking trojan or other malware designed to capture payment information or generate some form of income for the attacker.
3 Email Security Myths to Let Go
A large part of why organisations are scammed by cyber attackers is because they take a lax approach to email security. This, in turn, often stems from believing in email security myths such as the ones here:
1. Your Service Provider Has Your Back
One of the biggest myths people and organisations believe is that their service providers, whether it’s their cloud host or email platform provider, will take care of their email security. While it’s true that most companies take steps to keep their platforms as secure as possible, you can’t expect them to be responsible for errors on the user side of things.
For example, if you use Gmail via Google Workspace but opt out of multi-factor authentication, you can’t blame Google for it.
2. Hacking Threats Are Overblown
According to the Hiscox Cyber Readiness Report of 2019, the average cost of cyber security attack on a business is $200,000 — enough money to put smaller companies out of business for good.
Cyber security is a serious issue that you should not take lightly. And hackers are only getting smarter. It’s safe to say that attackers are becoming more targeted and researching potential victims at both the business and individual levels.
3. Small Businesses Don’t Have to Worry
Cyber attackers aren’t concerned about the size or type of your organisation — anyone with remote access to email is a potential target. In fact, 43% of cyber attacks target small businesses, according to research by Accenture. Worse, only 14% have the means to protect themselves.
At Optimising IT, we’ve seen large corporations with thousands of employees and SME organisations, with anywhere from 50 to 500 staff, compromised in this way.
Email Security Practices to Be Part of the 8% of Safe Organisations
Fortunately, it’s not all bad news. You can implement many technical and procedural controls to reduce the likelihood of this happening to your business.
We have two simple solutions that will go a long way towards protecting your organisation’s emails.
1. Staff Training and Awareness
Education and training are the keys to eliminating user error.
Ultimately, if nobody clicks on a phishing link or opens a bad attachment, your company won’t be exposed to attacks. Of course, this is easier said than done, especially if you receive an email with an attachment from an email address you frequently interact with that’s been compromised.
This is where the next tip comes in.
2. Implement Multi-Factor Authentication (MFA)
MFA is an advanced way of authenticating the identity of users in your email system.
Even if someone does end up stealing an employee’s email username and password, MFA will still keep them out of your system by requiring them to verify their log-in via a separate secure device, such as a smartphone held by a manager.
Need Help with Your Email Security?
Let the team At Optimising IT provide your business with personalised and comprehensive cyber security solutions. Our award-winning IT consultancy and managed cloud services will secure your IT infrastructure from end to end, protecting you from phishing attacks and other cyber security scams.
Get in touch today to learn how you can improve your email security and reduce the risk of this happening to your business.












